- A simpler integration
- Less data being passed
- No polling needed
- Updates only sent when changes happen
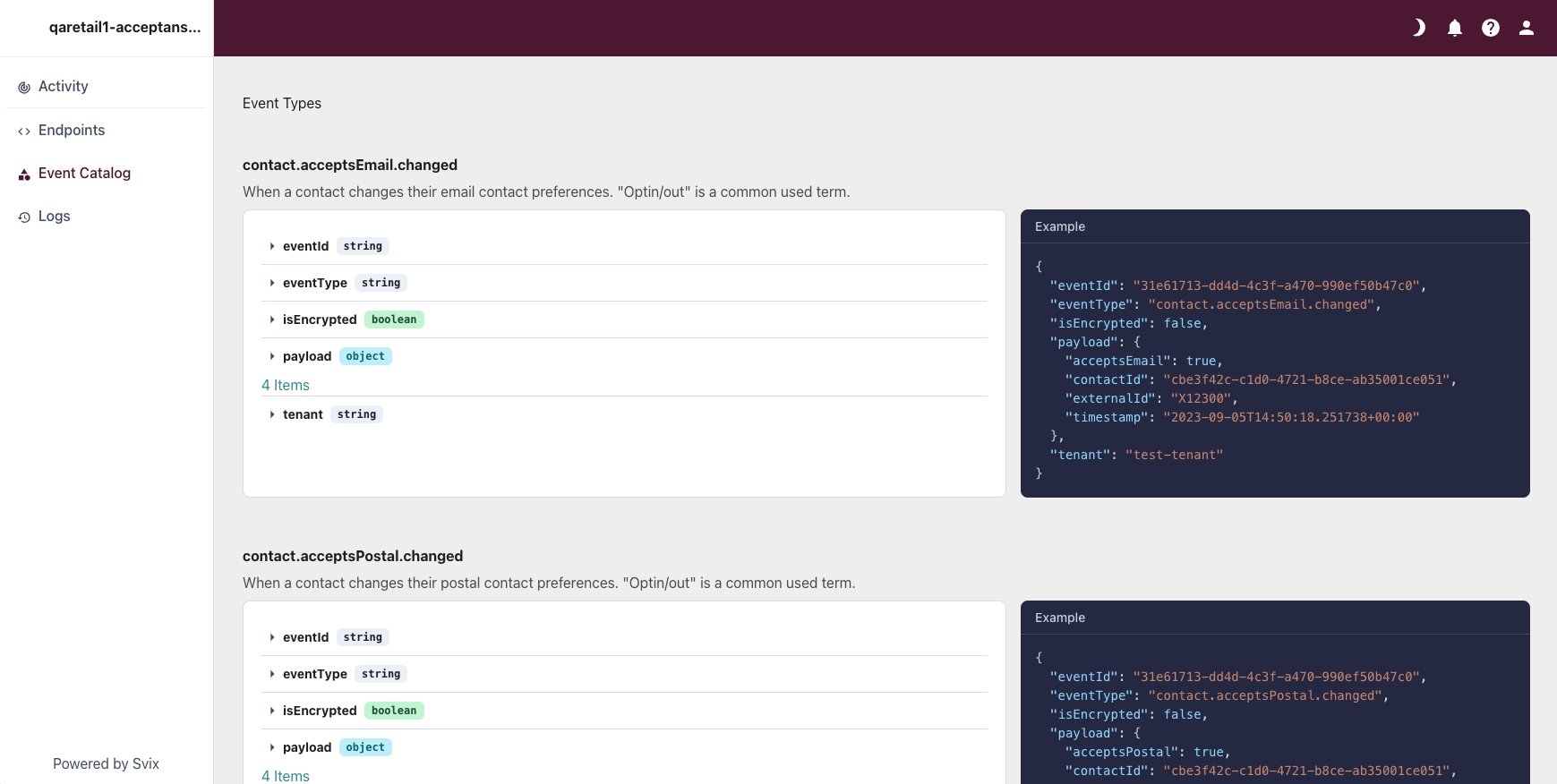
Webhooks currently available
Currently these webhooks can be used in Engage:Contact preferences - email
Contact preferences - email
This webhook with the ID
contact.acceptsEmail.changed is triggered whenever the acceptsEmail preference changes for an already existing contact.Contact preferences - sms
Contact preferences - sms
This webhook with the ID
contact.acceptsSms.changed is triggered whenever the acceptsSms preference changes for an already existing contact.Contact preferences - postal
Contact preferences - postal
This webhook with the ID
contact.acceptsPostal.changed is triggered whenever the acceptsPostal preference changes for an already existing contact.Points - add
Points - add
This webhook with the ID
loyalty.addPoints is triggered whenever points are added to a contact via the Engage UI or through an automation. The transaction is sent in the webhook.Points - balance updated
Points - balance updated
This webhook with the ID
point.balance.updated is triggered whenever a contact’s point balance has changed.Vouchers - created
Vouchers - created
This webhook with the ID
reward.voucher.created is triggered whenever a reward voucher is created for a contact.Requirements for webhooks
Here are the various requirements you’ll need to implement a webhooks solution.Basic client requirements
To receive webhooks from Engage you will need to develop and deploy a web service. This is basically an API with a POST endpoint. It’s common to use one service for all webhooks and then distributes the incoming events internally to your different systems. Your web service must be accessible over the internet. Fixed source IP addresses can be used if your endpoint is behind a firewall or NAT. There should be no authentication at the receiving endpoint. Instead, you’ll verify that the events received are sent from Voyado Engage using signatures and a shared signing secret. The service you provide must be able to scale with the load. Voyado’s webhooks service provider Svix has good documentation on how to consume webhooks.How to consume webhooks using Svix
Technical client requirements
You, the client, must develop functionality to verify the webhooks are from the correct sender.How to verify payload using Svix
Code libraries available for Svix
Read more soft identification
Legal requirements
Read about GDPR sub-processors
Setting up webhooks in Engage
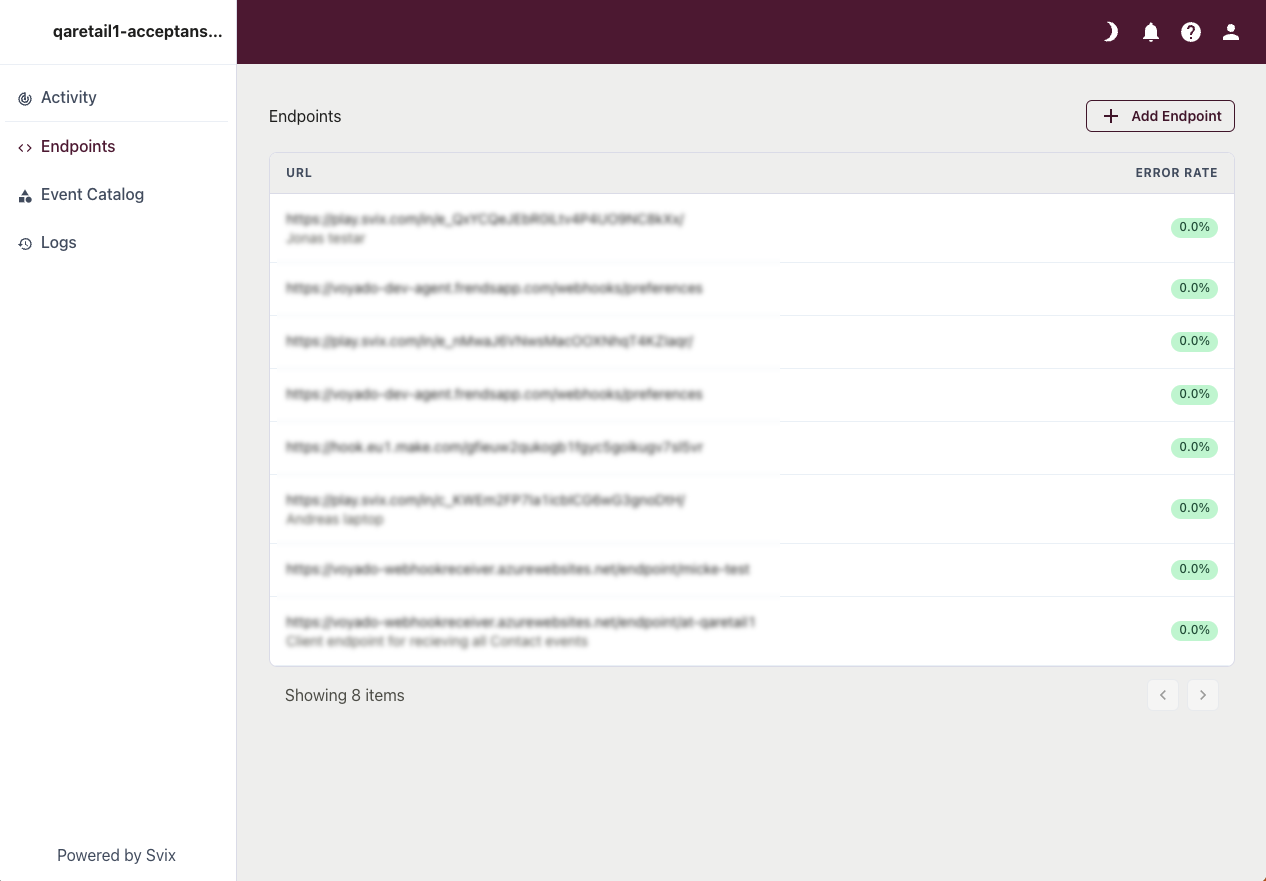
Once you have created your webhooks, you’ll need to set them up in Engage. The steps are:Enable webhooks in Engage
Contact your Voyado account manager to enable webhooks in your Engage instance. Depending on your agreement, a supplement might be required. The webhooks module must then be activated in the Engage back-end, and the correct permissions granted to users.
Configure client endpoint
Now you’ll configure the client endpoint in the Engage UI. Start by going to Administration/Webhooks Dashboard to see all the Webhooks already set up. Select + Add Endpoint to add another.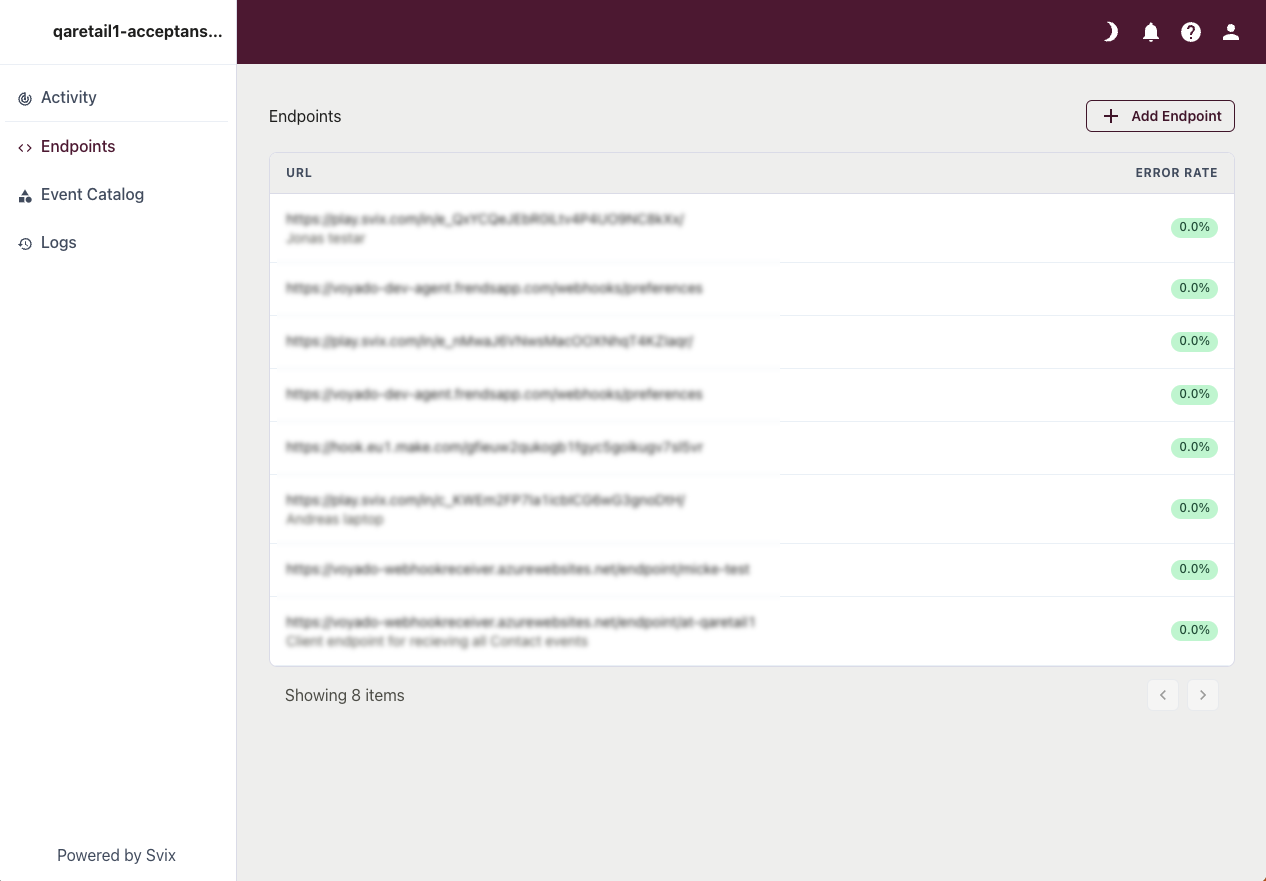
Choose events to use
After adding your endpoint, select it and then choose which event you want to send to it: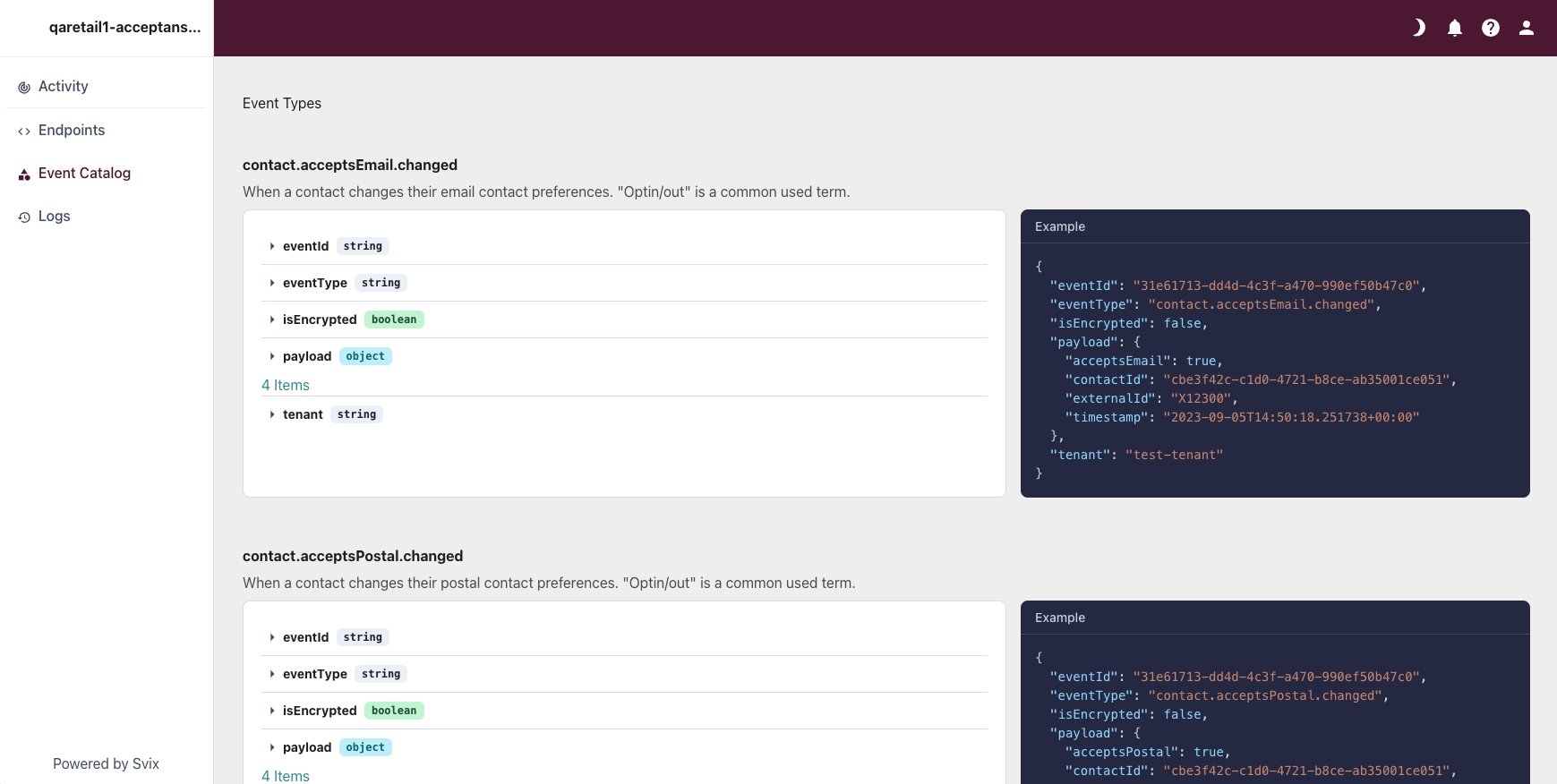
Add verification and encryption
Get the Signing Secret used for verification, as well as the Payload Encryption Key (if you are using it) from your Voyado account manager. When sending these to somebody else, be careful to use the same trusted method as when sharing API-keys. The signing secret is created and handled by Svix, and can be rotated if needed.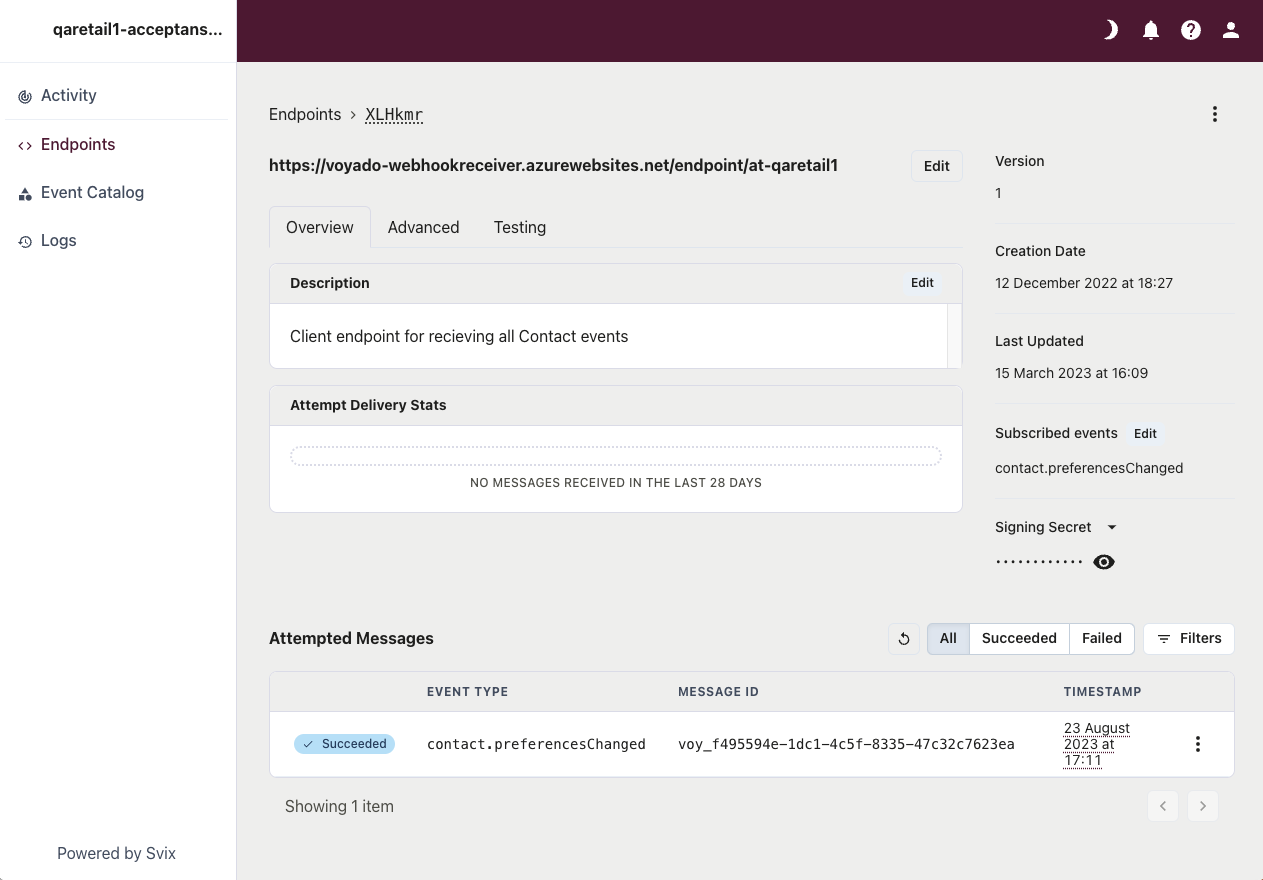
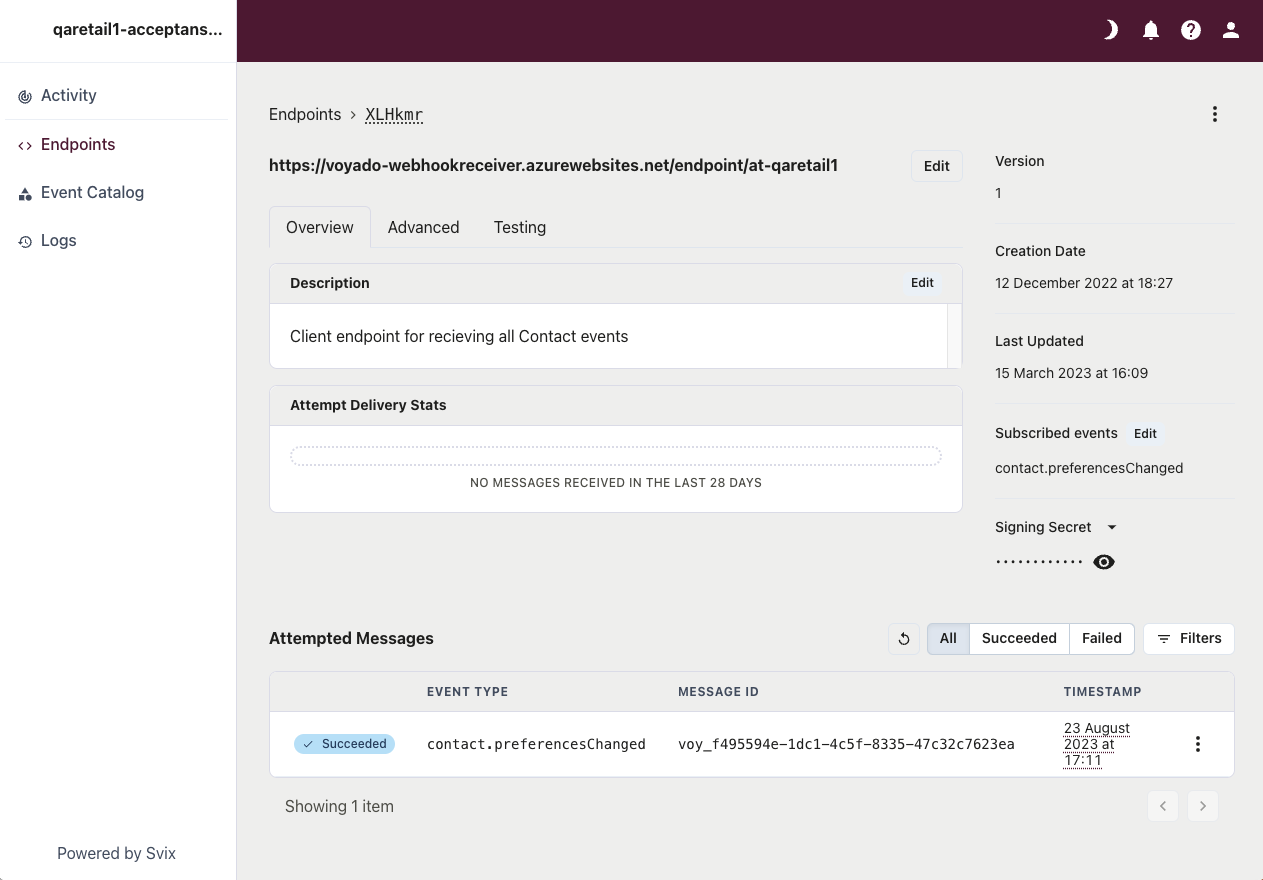
Test your webhook
You can use the “Testing” functionality in Svix to send test-events to the endpoint. Check the log for errors.
Configure a rate limit (optional)
If you need it, configure a rate limit so the client endpoint can handle the load.
Security layers
The security involved in using the webhooks solution can be seen as many nested layers.- The webhook itself: No security.
- Signing the webhook message with Signing Secret: The recipient can verify that the webhook comes from Voyado. The Signing Secret is found in the portal (meaning that Svix controls it). The client can rotate the key whenever they want.
- IP lock: Messages can only be accepted from specific IP addresses.
- Payload encryption: All data from Engage is encrypted with a key that only Voyado and the client have. It is configured in Engage, meaning that Svix cannot read any of the data that passes through it.